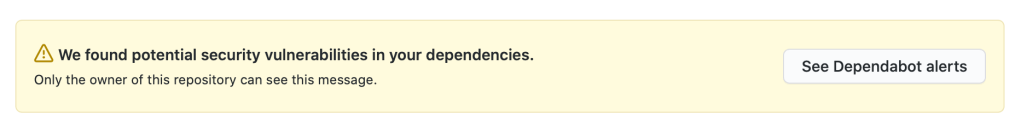
It can be a little alarming at first to see a glaring message from Github warning you of potential security vulnerabilities in the dependencies within your package.json file.
So we know that GitHub sends Dependabot alerts when they detect vulnerabilities affecting your repository. But what exactly do they mean by “vulnerability”?
A vulnerability is a problem in a dependency project’s code that could be exploited to damage the project and thus other projects that use its code (like yours). Vulnerabilities vary in type, severity, and method of attack.
When your code depends on a package that has a security vulnerability, this vulnerable dependency can cause a range of problems for your project or the people who use it.
Letting Github Handle Alerts
You can navigate to your security alerts by clicking the “See Dependabot alerts” button in the yellow warning message at the top of the repository.
Or go to the Security tab > Dependabot alerts
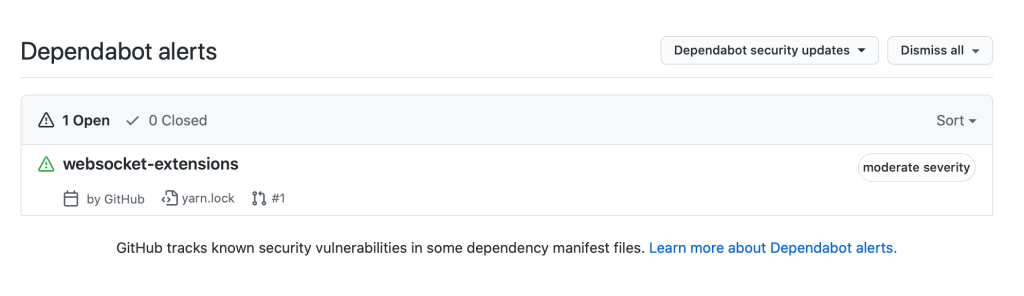
You should see an alert(s) like this:
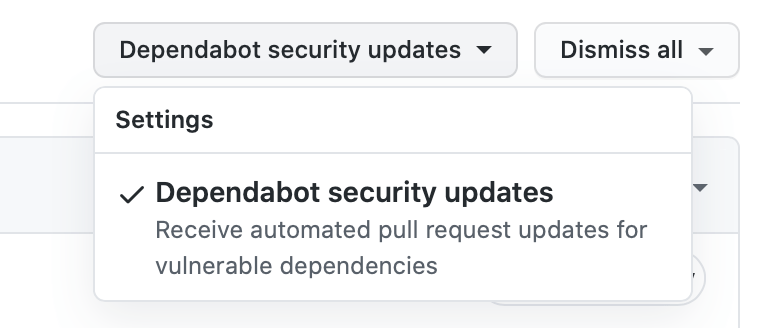
Make sure you have the “Dependabot security updates” option set to allow Github to automatically initialize pull request updates for vulnerable dependencies:
When Github has found a solution to the vulnerability, it will put a notification in the Pull Request section of your repository. Navigate to this section and you should see a pull request put here by Github:
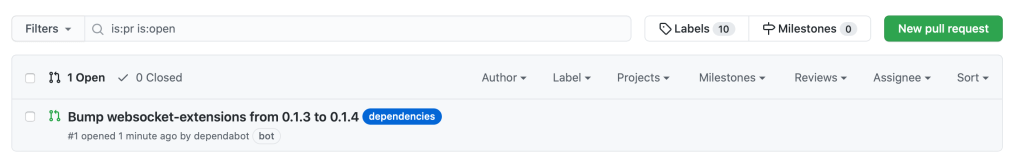
Merge this pull request into your project and the problem should be solved!